Your Current SOC Model Isn’t Keeping Up
Your Current SOC Model Isn’t Keeping Up
Defend at Machine Speed.
Make your SOC Agentic in 30 Days.
Traditional SIEM, MDR and XDR models are trapping your team in a cycle of endless triage. Built for a different era, they rely on human-speed workflows to fight machine-speed AI attacks, leaving you with massive blind spots and an exhausted security team.
Netenrich combines a digital workforce of AI Agents, proactive posture analytics, and dedicated human expertise. We eliminate the operational noise that drains your resources.
We stop managing alerts and start managing your actual risk.
 Exciting News from Google Cloud Next 2026
Exciting News from Google Cloud Next 2026
Netenrich Named Google Cloud Partner of the Year
For Security: Managed Security Service Provider — North America
Netenrich was recognized for helping joint customers achieve measurable security outcomes by combining its engineering-led approach to detection, response, and risk prioritization with deep AI and agentic capabilities natively built on Google Cloud.
Its Resolution Intelligence Cloud™ platform leverages agentic AI to automate complex security workflows, enabling organizations to move beyond alert-driven security toward efficacy-driven, outcome-oriented security operations.
Agentic Security. Proven at Scale. Recognized by Google.
Chosen by Google for turning 210+ security operations into measurable, real-world outcomes—not just alerts and activity.
“The Google Cloud Partner Awards honor the strategic innovation and measurable value our partners bring to customers. We are proud to name Netenrich a 2026 Google Cloud Partner Award winner, celebrating their role in driving customer success over the last year.”
Kevin Ichhpurani
President, Global Partner Ecosystem and Channels, Google Cloud
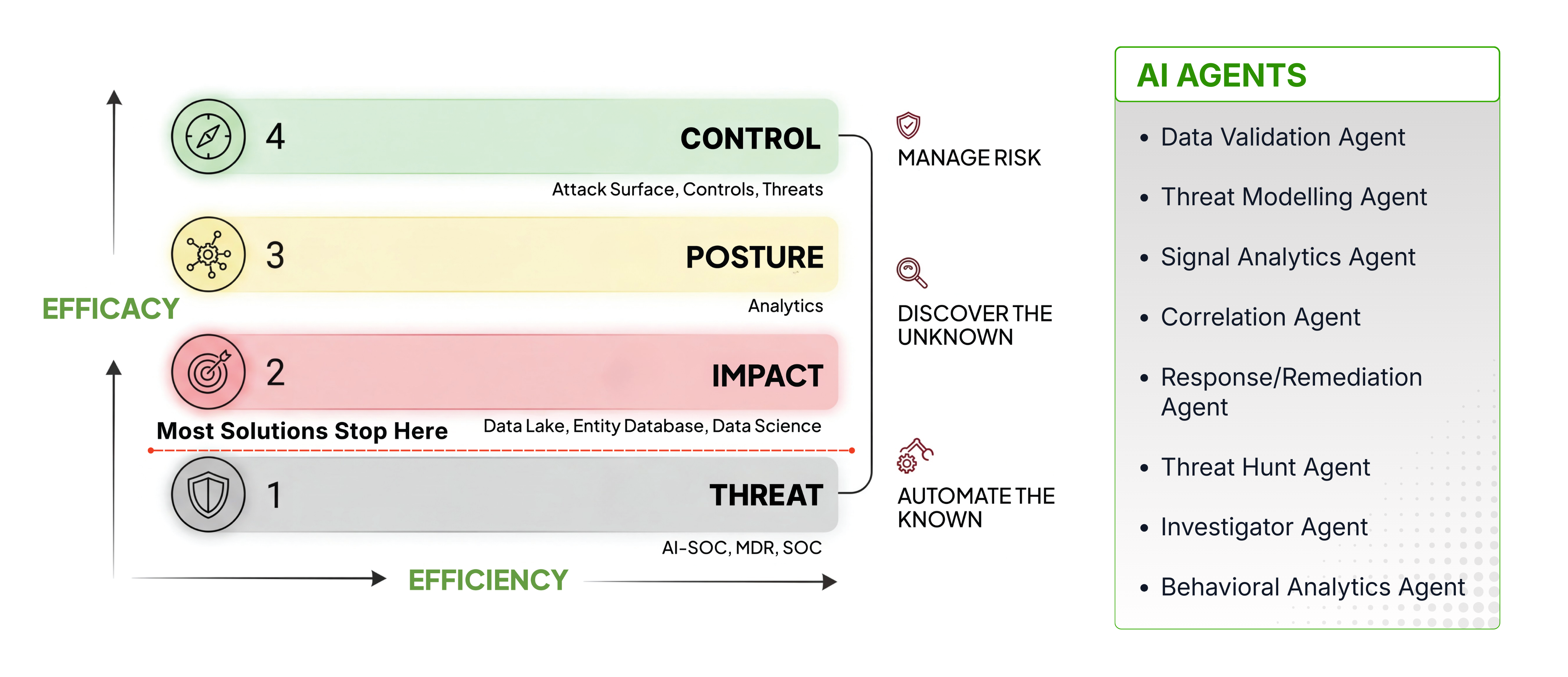
Activity vs. Outcomes: From Threat Overload to Agentic Control
Netenrich Delivers Impactful Outcomes Across Four Dimensions
Most security platforms (SIEM, MDR, XDR, and AI SOC) operate almost entirely in the Threat dimension, optimizing speed and efficiency while lacking business ontology.
This is where most security operations plateau, no matter how much automation or AI is added.
Netenrich helps move security up the curve; from threat awareness to situational awareness beyond threat across Impact, Control, and Posture alignment, where real cyber risk is understood and managed.
Netenrich utilizes Agentic AI to bridge the gap between risk and operations, accelerating the evolution toward Adaptive Cyber Risk Security Operations.
Through the Resolution Intelligence CloudTM outcome-driven approach, it enables enterprises to not just feel safe, but to be prepared and resilient.
Prepared Isn’t a Buzzword. It’s Measurable.
See what happens when your SecOps shifts from reactive firefighting to proactive, intelligent defense with Netenrich.
The Four Dimensions of the Netenrich Approach
Threat - From IOCs to Behavioral Coverage
Threat-focused security operations are not enough. Traditional SOCs reduce alerts to stay functional, at the cost of coverage.
Netenrich intentionally expands visibility, ingesting and processing greater than 30x more threat signals and behaviors than traditional SIEM or MDR environments can handle.
Every security-relevant behavior is captured as a signal and correlated over time (not filtered away) creating complete behavioral visibility without overwhelming analysts.
Impact - From Alert Queues to Business Risk Prioritization
Seeing more signals only matters if you know which ones matter most.
Netenrich applies the LIC Model (Likelihood × Impact × Confidence) to every correlated signal, converting raw activity into business-impact–aware risk decisions.
- Likelihood reflects adversary capability and attack stage
- Impact is derived from asset criticality (“Crown Jewels”) and loss potential (blast radius)
- Confidence adjusts prioritization based on signal fidelity and correlation strength
This replaces first-in/first-out alert handling with risk-weighted prioritization, ensuring teams address business exposure before technical noise.
Posture - From Reactive to Proactive Security
Most security failures happen without alerts, because the controls responsible for alerting are broken, missing, or misconfigured.
Netenrich continuously validates posture at runtime, surfacing scenarios such as:
- Ghost assets missing security telemetry
- Attack surfaces and assets exposed to current global threats
- Control drift and non-permissive configuration changes
- Attack surfaces with exposures and vulnerabilities due to misconfigurations
- Risky but "authorized" behaviors that are risky
- Silent failures and abnormal behaviors that are risky
- Long and slow attacks over a 12-month period
This exposes the Illusion of Coverage, replacing assumed protection with evidence of what is actually working
Control - Align Attack Surface, Controls, and Threats
Operating across Threat, Impact, and Posture enables continuous alignment of:
- Attack Surface (what exists and what matters)
- Controls (what is effective right now)
- Threats (what adversaries are actually doing)
This alignment projects attacker progression paths and allows teams to disrupt the kill chain before impact, not after breach.
The Security Outcomes
Your Business Demands
Security outcomes don’t improve by closing tickets faster. They improve when security can see more, understand more, and act with context.
Netenrich delivers outcomes that are structural, measurable, and sustained; because it operates across Threat, Impact, Control, and Posture with continuous alignment.
Improvement in Detection Coverage
Coverage expands because Netenrich does not suppress alerts or signals. It ingests and reasons over far more security data, revealing blind spots, drift, and attack activity others never see.
Reduction in Manual Workload
Agentic AI reasons over signals, context, and risk; so humans focus on judgment, investigation, and strategy, not queue processing.
Reduction in Total Security Cost
Consolidating SIEM, SOAR, and Threat Intel into a single autonomous stack drastically cuts tool sprawl and ingestion waste.
AI Autonomy Rate
Autonomous AI agents handle 98% of the operational noise and routine alert processing, which frees human analysts to focus exclusively on the 2% of strategic decisions that matter most.
Improvement in Control Health
Continuous validation eliminates silent log failures and configuration drift.
Mean Time to Escalate
Moving at machine speed from initial detection, through AI correlation, to high-fidelity containment.
From Threat Awareness to Situational Awareness
Threat awareness tells you what exists in the world. Situational awareness tells you what matters in your environment and what to do about it.
VULNERABILITY EXPOSURE
Legacy tools bury you in "Critical" CVEs that don't matter. We isolate the threats that actually bankrupt you.
- Threat Awareness: A ‘Critical’ CVE is being actively exploited in the wild.
- Situational Awareness: This CVE targets your primary revenue engine where a compensating control is broken and lateral movement is wide open.
- The RiskOps Verdict: This needs immediate action. We prioritize this specific mitigation now, while deprioritizing the same CVE on isolated, non-critical assets that legacy tools would tell you to chase.
IDENTITY COMPROMISE SEQUENCE
Stop looking for "anomalous needles" in a haystack of false positives. Start killing the thread.
- Threat Awareness: A single anomalous sign-in alert for a privileged user.
- Situational Awareness: Our Agentic AI correlates that sign-in with silent mailbox rule creation and subsequent data movement over time.
- The RiskOps Verdict: This isn't an "anomaly", it is an active account compromise and a direct breach path. We escalate this as a high-impact action item immediately to disrupt the adversary before the data leaves the building.
DATA MOVEMENT
THE MDR NOISE: "THREAT AWARENESS"
- Signal: Large outbound data transfer.
- Problem: One of 10k alerts, ignored as "routine sync".
THE RISKOPS TRUTH: "SITUATIONAL READINESS"
- Signal: Identify that the transfer originates from a High-Value Asset.
Exposure: Agentic AI workforce detects that the transfer bypassed a DLP Policy (a Silent Control Failure) and maps it to historical Exfiltration Behavior.
The Math: Using the LIC Scoring Model, we calculate a high-confidence Risk score: Risk = (Likelihood × Impact) × Confidence.
THE ULTIMATUM: "IMMEDIATE NEUTRALIZATION"
- The Action: Treat as a High-Risk Exposure, not a ticket.
- The Action: Zero-Tolerance Neutralization. Our Agentic AI investigators autonomously gather evidence and initiate containment before material impact occurs, shifting your team from "Alert Factory" workers to Strategic Risk Supervisors.
LOW-AND-SLOW CREDENTIAL MISUSE
- Threat Awareness:Valid use of cloud credentials.
- Situational Awareness:The same long-lived credentials are accessed from multiple geographic regions over time, signaling credential compromise and lateral movement.
Action: Rotate credentials and disrupt the attack path before exfiltration.
CONTROL DRIFT
- THE MDR TRAP: No alert fired. In a legacy SOC, silence is treated as safety.
- THE SITUATIONAL TRUTH: A production log source silently stopped shipping data. This is a Silent Failure.
THE ULTIMATUM: Restore telemetry immediately before exposure compounds.
Math: Risk = (Likelihood x Impact) x Confidence. When Confidence drops, Risk skyrockets
AUTHORIZED BUT RISKY BEHAVIOR
- MDR BLIND SPOT: Admin action detected. Marked "Authorized"
- SITUATIONAL TRUTH: Cloud Admin spinning up infra outside Change Control. This is Shadow Ops.
Action: Trigger validation and enforce policy before abuse escalates.
SEVERITY WITHOUT CONTEXT
- Threat Awareness: High-severity alert triggered.
- Situational Awareness: The activity targets a low-impact endpoint and matches the user’s role, while a medium-severity signal elsewhere targets a crown-jewel system with weak controls.
Action: Deprioritize safely. Escalate what actually threatens the business.

Rethinking SecOps for a World That Never Stands Still
Traditional security operations are designed to respond to incidents. They optimize for alert handling, ticket closure, and after-the-fact investigation.
Netenrich manages cyber risk continuously, not just react to events.
Are you prepared right now, and can you prove it?
Cyber risk doesn’t live in tools or alerts, it lives in your environment.
Netenrich continuously maps your assets (attack surface), identities, controls, and threats into a living operational model, giving security teams a single, trusted view of what exists, what’s protected, and where real risk is emerging, right now.
From Your Environment Data to Operational Truth
- Unified Data: Security telemetry across cloud, identity, endpoint, network, SaaS, and applications is normalized into a single operational view of the customer environment.
- Contextual Risk Modeling: Signals are evaluated in context (asset criticality, control coverage, configuration posture, and attacker behavior) so risk is understood, not just detected.
- Continuous Risk Reasoning: Analytics continuously assess exposure, drift, and attacker movement as environments and threats evolve, eliminating blind spots between reviews.
- Actionable Workflows: Insights flow directly into validation, remediation, or escalation workflows; prioritized by real risk, not alert volume.
- Authoritative Operational Truth: Integrations enrich and act, but the environment model remains the trusted source for what exists, what’s protected, and what requires action; right now.
Netenrich unifies AI, data, and human expertise into one continuously improving security model.
A Digital Workforce of AI Agents for Agentic Security Operations
Instead of hiring more analysts, you deploy a coordinated system of AI agents.
Data Validation Agent
Ensures log integrity, detects silent failures, validates parsing health.
Threat Modelling Agent
Continuously validates detection pipelines and SOC health.
Signal Analytics Agent
Analyzes historical data to identify hidden patterns and slow-brewing attacks that real-time rules miss.
Correlation
Agent
Stitches signals into ACT-driven incident chains using LIC scoring.
Behavioral Analytics Agent
Establishes baselines for user and asset behavior to identify high-risk deviations and anomalies.
Investigator
Agent
Automates deep investigation, maps kill chains, drafts verdicts.
Threat Hunt
Agent
Proactively hunts unknown threats using behavior and model context.
Response/Remediation Agent
Executes automated playbook actions to instantly neutralize threats and isolate compromised assets.
The Blueprint For Readiness. Quantifying Security Outcomes.
Automate The Known: Kill The Alert Factory
Netenrich treats alerts as signals, not work items
Agentic AI continuously ingests, correlates, and reasons over tens of thousands of behaviors per day, handling known patterns, repeat conditions, and routine investigations automatically.
This allows security teams to see everything without manually touching everything and focus human effort where judgment is required.
-
Classification by purpose: Log sources are categorized by investigative value, detection value, enrichment value, compliance value, or no-value; reducing cost without reducing coverage.
- Attack-surface–aware visibility: Alert/Signals are mapped to real attack surfaces (identity, endpoint, cloud, SaaS, network, hypervisor), not treated as generic events.
- Coverage clarity: Detection coverage is mapped to attacker techniques, and gaps are made explicit before adversaries find them.
- Decision-ready outcomes: Raw events are transformed into a small set of high-confidence action items through continuous correlation and optimization.
.webp)
Discover The Unknown: Hunt The Unseen. Eliminate The Stealth.
Not all risk announces itself. Netenrich goes beyond static detection rules by applying behavioral analytics and continuous threat hunting across extended time horizons, uncovering scenarios that evade traditional security operations.
We don't wait for alerts. We weaponize the ACT Framework (aligning Attack Surface, Controls, and Threats) to actively search for the scenarios legacy solutions miss:
- Low-and-Slow Execution: We map multi-stage kill chains across months of data, not just hours.
- Access Hijacking: We expose the abuse of legitimate access before it turns into a headline.
- Ghost Techniques: We find the emerging threats that evade static signatures by hunting behavioral intent.
- And more such scenarios
Unknown risk isn't a problem, it’s the target. We replace subjective feelings of safety with mathematical Situational Awareness.
- Posture-driven threat discovery: Posture weaknesses are directly mapped to relevant threat techniques and adversary behaviors.
- Multiple hunting strategies: Hunting is continuous and multi-modal; combining behavioral analytics, threat intelligence, exposure analysis, and signal correlation.
- Risk register with intent: A living register of the most critical exposures across identity, endpoint, cloud, SaaS, network, and infrastructure; prioritized with clear remediation guidance.
The Core Engine:
The Netenrich DNA.
Netenrich isn’t a toolset or a service wrapper.
It’s a disciplined operating model, engineered to deliver sustained cyber risk outcomes, even as environments, attack surfaces, and threats continuously change.
Why Customers Choose Us
- Efficacy First: Security measured by risk reduction, not alert throughput or ticket volume.
- Measurable Outcomes: Readiness that can be quantified, tracked, and demonstrated over time; not inferred from dashboards.
- Continuous Adaptation: Defenses evolve as business velocity, attack surfaces, and adversary behavior change.
Cross Discipline Team DNA
- SRE and Digital Ops DNA
Continuous validation, reliability checks, and feedback loops are built in to prevent drift. - Security Engineering Rigor
Detections, controls, and response logic are engineered systems, not ad hoc rules. - Data Science Discipline
Prioritization is driven by risk-based scoring, not static High/Medium/Low labels.
Engineering Approach to RiskOps
- Data Engineering at Scale: High-fidelity telemetry and long-horizon signal retention across environments.
- Detection and Behavioral Engineering: Coverage aligned to real attacker behavior, not just known signatures.
- Quantified Response Engineering: Actions driven by likelihood, impact, and confidence, not alert volume.
Most vendors address one dimension in isolation. Netenric cuts across all four pillars operate on the same data, context, and decision logic, continuously.
Make your SOC Agentic in 30 Days
Stop fighting machine-speed AI attacks with human-speed triage. Reduce ingestion costs, increase detection coverage, and eliminate manual triage; while securing your cloud and production environments at scale.
Delivering Real-world
Outcomes for Global Enterprises
Don’t take our word for it – hear directly from our customers about how we transformed their security operations.
“Netenrich gave us clarity we didn’t have before. By collapsing dozens of disconnected workflows into a small number of risk-driven operating paths and materially expanding our detection coverage, we moved from managing alerts to managing risk. We now operate with far greater confidence and precision.”
Kumar Palaniappan
CISO, Citrix (Cloud Software Group)
“With Netenrich and Google SecOps, our team focuses on what actually matters — meaningful investigations and risk decisions, not chasing noise. We can now explain our security posture clearly to leadership and show how our controls, detections, and response align to business risk.”
Harsh Jha
CTO, Nuvama Group
“Netenrich didn’t just solve today’s problems. They helped us adopt an operating model that scales as our environment changes. Our security operations are now adaptive, resilient, and built for long-term risk management.”
CISO
Healthcare Organization
Success Stories & Resources


Case Study
Citrix and Cloud Software Group Transforms Security Operations with Netenrich Adaptive MDR
![Digital Marketing Banner[10]](https://netenrich.com/hs-fs/hubfs/Digital%20Marketing%20Banner%5B10%5D.png?width=800&height=421&name=Digital%20Marketing%20Banner%5B10%5D.png)
![Regional Bank Banner[88]](https://netenrich.com/hs-fs/hubfs/Regional%20Bank%20Banner%5B88%5D.png?width=800&height=421&name=Regional%20Bank%20Banner%5B88%5D.png)
![Healthcare Banner[47]](https://netenrich.com/hs-fs/hubfs/Healthcare%20Banner%5B47%5D.png?width=800&height=421&name=Healthcare%20Banner%5B47%5D.png)