Maturing Cyber Defenses on the 2024 Horizon
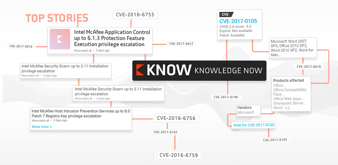
As rising digital connectivity expands the cyber risk plane in 2024, threat actors continue co-opting innovations to pioneer more virulent extortion...

As rising digital connectivity expands the cyber risk plane in 2024, threat actors continue co-opting innovations to pioneer more virulent extortion...
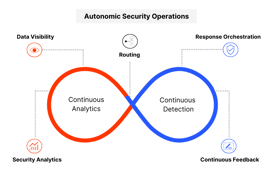
So, what’s a SOC? Some still believe they need a physical SOC building, where they can see, touch, and manage servers. Others feel it’s necessaryto...

In the ever-evolving landscape of cyber threats, it's not surprising that organizations are expanding their cybersecurity budgets to fortify their...
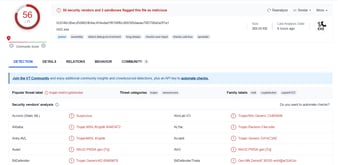
This article is not an in-depth reverse-engineering analysis of a ransomware variant. Rather, it discusses the methods and different techniques used...
Beaconing attacks can be difficult—but not impossible—to detect. The more you know about these stealthy attacks, the better you’ll be able to uncover...

With the rise of generative AI models, the threat landscape has changed drastically. Now, recent activities on the Dark Web Forum show evidence of...

















The best source of information for Security, Networks, Cloud, and ITOps best practices. Join us.